Identity & Access
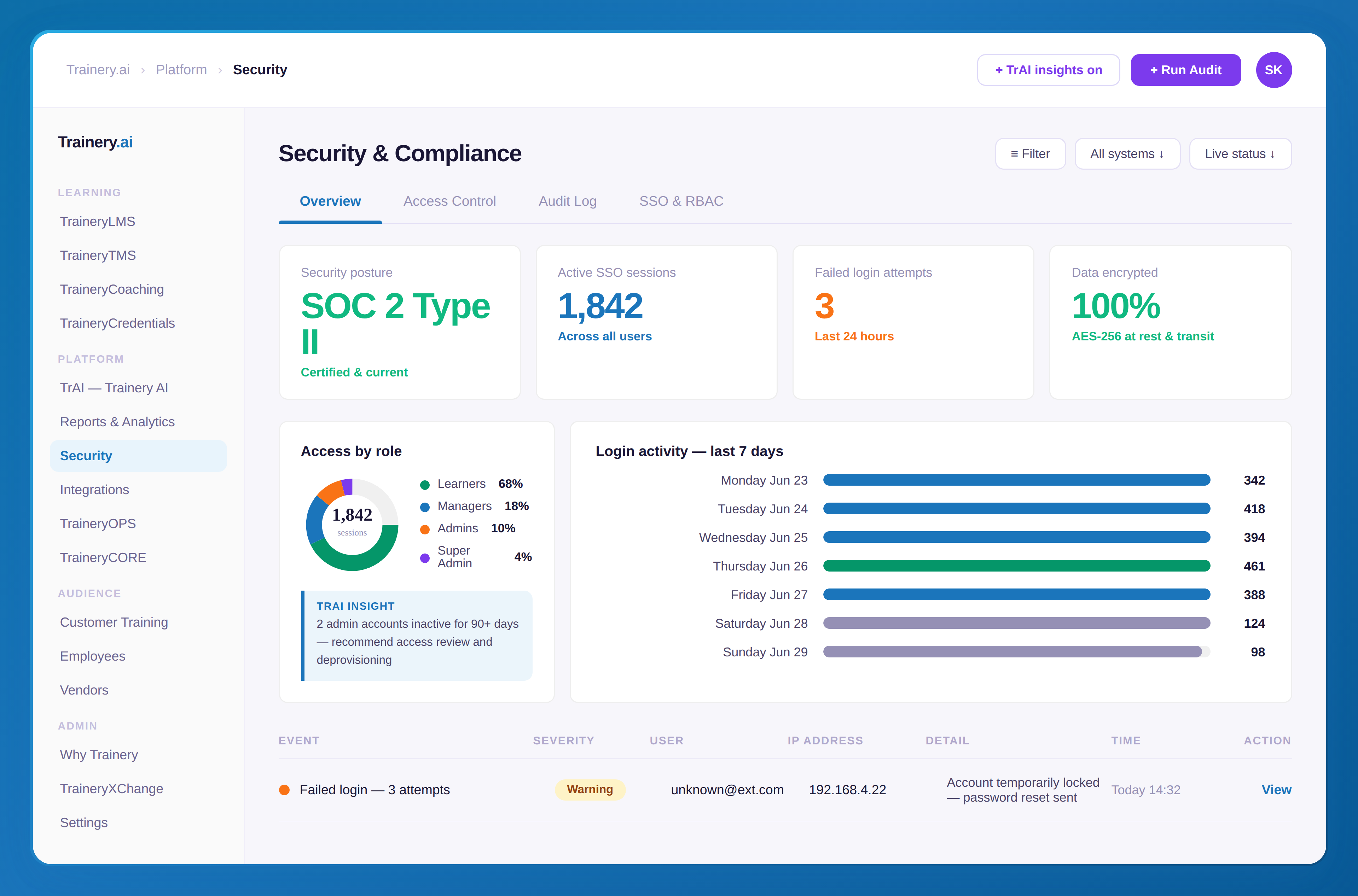
Granular role-based access controls across every Trainery module — from learner to admin. Single sign-on with SAML 2.0 means employees use their existing credentials, with no separate password to manage.
RBAC across all modules and data
SSO via SAML 2.0 / Okta / Azure AD
Multi-factor authentication (MFA)
Data Protection
All data encrypted at rest and in transit using AES-256 and TLS 1.2+. Backups are encrypted and geographically redundant. Data retention policies are configurable to match your compliance requirements.
AES-256 encryption at rest
TLS 1.2+ encryption in transit
Compliance & Audit
Full audit logs track every admin action, user change, and data access event. Reports are exportable for compliance reviews, internal audits, and regulatory requirements.
Immutable audit logs for all actions
Exportable compliance reports
Infrastructure & Isolation
Multi-tenant architecture with strict data isolation — your data never shares compute or storage with another organization. Designed for enterprises and regulated industries where data separation is non-negotiable.
Full tenant data isolation
Dedicated infrastructure options
Penetration testing program

.svg)
.svg)
.svg)


.svg)
.svg)

.svg)

